Replace Magic Numbers in Documentation With Qualitative Language
Every framework says '43 tools' and becomes wrong the moment you add tool 44. Here's a controversial but practical solution: ban all hardcoded counts.
Every framework says '43 tools' and becomes wrong the moment you add tool 44. Here's a controversial but practical solution: ban all hardcoded counts.

security
Build a complete vulnerability remediation workflow using SSH and structured phases - no enterprise SOAR platform required.
Most AI QA catches errors after generation. Verification-first aims to ground reviews in external facts - here's how to implement it and its limitations.
After a year of industry adoption and security disclosures, here's the data-driven analysis of MCP's real costs: up to 236× token inflation, 9.5% accuracy loss, and critical CVEs. Plus: why I chose direct VPS wrappers instead.

framework
How a PreToolUse hook recommends AI models based on keyword detection - suggesting Opus for complex problems, Grok for review, Haiku for validation. Soft guidance, not enforcement.
framework
Why I chose 'adjacent' over 'augmented' and what it means for human-AI collaboration. The philosophy behind the framework.
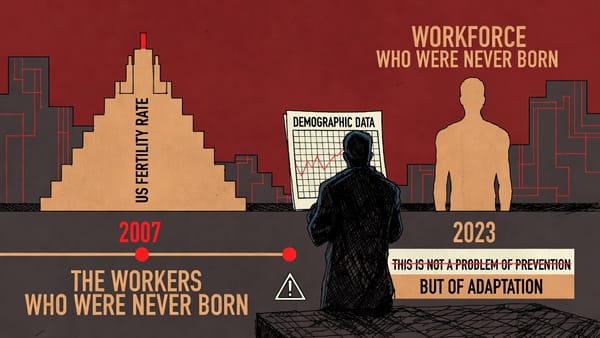
US fertility fell below replacement in 2007. The workers who would sustain our economy were never born. We're not preventing a crisis - we're adapting to one.

Step-by-step guide to measuring token counts with tiktoken. Validate efficiency claims, build your own measurement framework, and test your Code API wrappers.
framework
Store tool output locally, return summaries, read full data on demand. A pattern applied across 68 VPS security tool wrappers.
framework
How a PreToolUse hook could surface existing tools when AI agents attempt to create new scripts—and why I haven't implemented it yet.

How I implemented parallel task orchestration using Claude Code's new async subagents feature for concurrent multi-agent workflows.
infrastructure
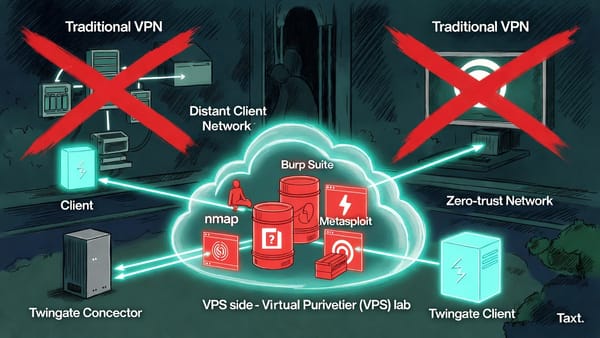
How to use Twingate's zero-trust architecture with Docker containers to conduct security assessments against private networks from anywhere - including the gotchas that'll save you hours of debugging.