
security
Close-Loop Vulnerability Remediation: Multi-Phase Workflow from Finding to Validation
Build a complete vulnerability remediation workflow using SSH and structured phases - no enterprise SOAR platform required.
Defensive security, penetration testing, and risk assessment—augmenting human expertise through structured methodology and hands-on practice.

security
Build a complete vulnerability remediation workflow using SSH and structured phases - no enterprise SOAR platform required.
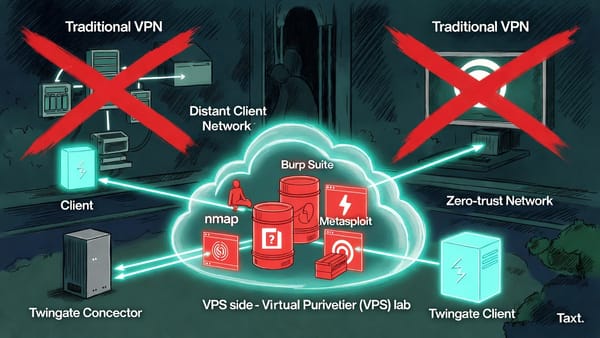
infrastructure
How to use Twingate's zero-trust architecture with Docker containers to conduct security assessments against private networks from anywhere - including the gotchas that'll save you hours of debugging.

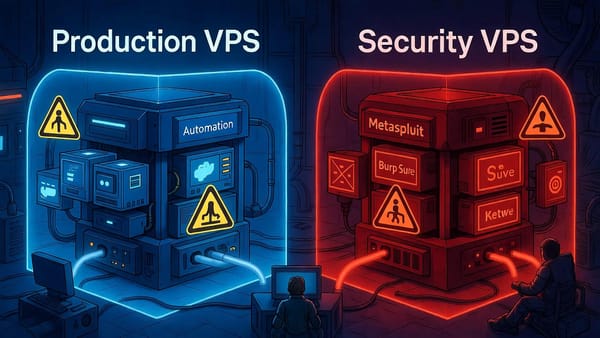
compliance
Most VPS providers ban pentesting. Here's why I use a dual-VPS architecture and a comparison of 7 providers with verified December 2025 pricing and policies.

career
Deploy security testing infrastructure rapidly with API automation. Real workflow for consultants using VPS, Twingate zero-trust access, and Docker containers.
infrastructure
How to deploy security tools across VPS instances with zero public exposure using Twingate and Docker. Complete 7-step workflow with validation procedures for production and testing environments.

security
Implementing defense-in-depth across dual VPS instances with 7 security layers. Production (Hostinger) prioritizes availability, security testing (OVHcloud) prioritizes lockdown.
infrastructure
Run security tools remotely, get summaries back. Professional infrastructure at a fraction of the cost.