
security
From Pattern Scanner to Security Researcher: The Code Review Upgrade
The code review skill now runs four sequential passes — structural recon, pattern scanning, semantic data flow tracing, and self-verification with confidence ratings.
Defensive security, penetration testing, and risk assessment—augmenting human expertise through structured methodology and hands-on practice.

security
The code review skill now runs four sequential passes — structural recon, pattern scanning, semantic data flow tracing, and self-verification with confidence ratings.
security
Prompt injection isn't growing because attackers got smarter. It's growing because we keep adding capability without solving the underlying architectural problem.

security
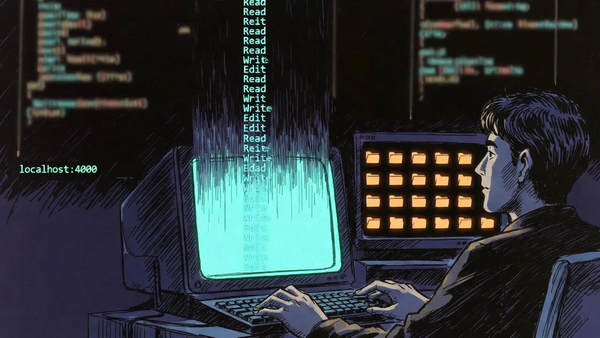
14 security vulnerabilities found. 3 systematic sprints. 100% validation success. How systematic code review and sprint-based remediation transformed our framework from vulnerable to production-ready.
security
The market promises autonomous AI pentesters replacing humans. The reality is more nuanced. What AI pentesting actually is, what it isn't, and why adjacency beats replacement.
security
A systematic gap analysis against Claude Code security standards revealed dormant hooks, missing defense layers, and undocumented decisions. Here is what I found and what I fixed.

security
Security guidance with framework citations, not hallucinations. Meet /advisory—a skill that automates research BEFORE asking questions.
framework
Automated model ranking system aggregating benchmarks from four sources with zero data retention filtering.
culture
In 1943, C.S. Lewis warned of a philosophical crisis that's now arriving with AI. We've embraced moral relativism while building systems that require absolute moral certainty.

culture
From cybersecurity to plumbing, private equity uses identical playbook to consolidate fragmented industries. The result: higher prices, reduced competition, and consumers paying for financial engineering.
security
Introducing a new design pattern for developer tools: ephemeral observability. The IA Framework monitor skill demonstrates how architectural constraints create advantages for localhost AI development workflows.

security
Build a complete vulnerability remediation workflow using SSH and structured phases - no enterprise SOAR platform required.
infrastructure
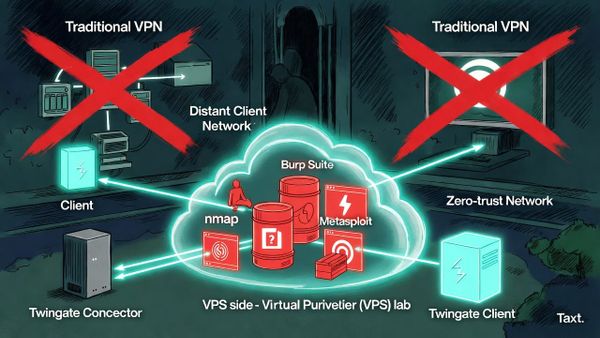
How to use Twingate's zero-trust architecture with Docker containers to conduct security assessments against private networks from anywhere - including the gotchas that'll save you hours of debugging.